VPN using Certificates
To keep things simple, and free, use CAcert as our Certificate Authority.
First, define a new CA on both SRX boxes. For now, the certificate revocation check will be disabled (for simplicities sake).
[edit security pki]
juniper@SRX210-1# show
ca-profile CACERT {
ca-identity CAcert;
revocation-check {
disable;
}
}
Download the CAcert class 3 root certificate from https://www.cacert.org/certs/root.crt. Note that these are downloaded on our UNIX box that the SRXes are being configured from.
juniper@unix-box:~$ wget https://www.cacert.org/certs/root.crt --2013-09-30 11:01:32-- https://www.cacert.org/certs/root.crt Resolving www.cacert.org (www.cacert.org)... 213.154.225.245, 2001:7b8:3:9c::245 Connecting to www.cacert.org (www.cacert.org)|213.154.225.245|:443... connected. HTTP request sent, awaiting response... 200 OK Length: 2569 (2,5K) [application/x-x509-ca-cert] Saving to: `root.crt' 100%[======================================>] 2.569 --.-K/s in 0s 2013-09-30 11:01:33 (90,6 MB/s) - `root.crt' saved [2569/2569] juniper@unix-box:~$
Copy the root cert up to the SRX boxen.
juniper@unix-box:~$ scp root.crt juniper@10.0.110.211: root.crt 100% 2569 2.5KB/s 00:00 juniper@unix-box:~$ scp root.crt juniper@10.0.110.212: root.crt 100% 2569 2.5KB/s 00:00
Load the root certificate up into the CA profile that was created ealier. Note that this is done from operational mode on the SRX.
juniper@SRX210-1> request security pki ca-certificate load ca-profile CACERT filename root.crt
Fingerprint:
13:5c:ec:36:f4:9c:b8:e9:3b:1a:b2:70:cd:80:88:46:76:ce:8f:33 (sha1)
a6:1b:37:5e:39:0d:9c:36:54:ee:bd:20:31:46:1f:6b (md5)
Do you want to load this CA certificate ? [yes,no] (no) yes
CA certificate for profile CACERT loaded successfully
juniper@SRX210-1> show security pki ca-certificate
Certificate identifier: CACERT
Issued to: CA Cert Signing Authority, Issued by: O = Root CA, OU = http://www.cacert.org, CN = CA Cert Signing Authority, emailAddress = support@cacert.org
Validity:
Not before: 03-30-2003 12:29
Not after: 03-29-2033 12:29
Public key algorithm: rsaEncryption(4096 bits)
juniper@SRX210-1>
Verify the root cert is OK on each SRX.
juniper@SRX210-1> request security pki ca-certificate verify ca-profile CACERT CA certificate CACERT verified successfully juniper@SRX210-1>
Create a public/private keypair on each SRX.
juniper@SRX210-1> request security pki generate-key-pair certificate-id srx210-1 size 2048 type rsa Generated key pair srx210-1, key size 2048 bits juniper@SRX210-1>
juniper@SRX210-2> request security pki generate-key-pair certificate-id srx210-2 size 2048 type rsa Generated key pair srx210-2, key size 2048 bits juniper@SRX210-2>
Generate a certificate signing request (CSR) for the keypair just created. The SRX is a bit finicky on the text in the subject name.
juniper@SRX210-1> request security pki generate-certificate-request certificate-id srx210-1 domain-name srx210-1.blackhole-networks.com subject "CN=srx210-1.blackhole-networks.com,OU=VPNs,O=Blackhole-Neworks,L=Stuttgart,ST=Baden-Wuerttemberg,C=DE"
Generated certificate request
-----BEGIN CERTIFICATE REQUEST-----
MIIC/jCCAeYCAQAwfDERMA8GA1UEAxMIc3J4MjEwLTExDTALBgNVBAsTBFZQTnMx
GjAYBgNVBAoTEUJsYWNraG9sZS1OZXdvcmtzMRIwEAYDVQQHEwlTdHV0dGdhcnQx
GzAZBgNVBAgTEkJhZGVuLVd1ZXJ0dGVtYmVyZzELMAkGA1UEBhMCREUwggEiMA0G
CSqGSIb3DQEBAQUAA4IBDwAwggEKAoIBAQDHvunt5EdaaamfowGEkPx2x+aWBS3w
+fs51kPrgRlMm3qTeUipyG2mZFeNENHrQ+IfHNq2TkRNPi7/8W9maRJJWjYgCXg9
jE0TK+OEEIXiGTeK182eO9wcbNLfx9xFbwtdLJk3+4R3OIKNAZGjXYAANdXheV6U
NCZKUFQzRkNnQxNVFnEFFdeqohf07EpX2fVWh3NOlF0eBfWD6eU6vPuaK+/E1E0e
YHlcYyZqIBctxpyKrwdEt2DKxu2j4gnJqF/01z03431FhncsPHMFUQVQH/mgIGOb
9wZCaieF4iSujLhxXtBEvmu95mNtwqlf5PkmcRxcwbrQwnP7avMROlj5AgMBAAGg
PTA7BgkqhkiG9w0BCQ4xLjAsMCoGA1UdEQQjMCGCH3NyeDIxMC0xLmJsYWNraG9s
ZS1uZXR3b3Jrcy5jb20wDQYJKoZIhvcNAQEFBQADggEBAEot0paMNY5lyLGmFAVy
EN79+TMVRio5GrKbWwR3noiYSEz7V29sEwfWibOw2TnjxblyNzK7IQIIcC8Qp/4T
c6fIlcG7TKSQo3bRsG7ghiiuXdfmuqaf7U/HnmYSTA4pK5o8nL2xtQuPan1VCATA
XhgOLcKTLrVZxWpfKziMgCxe7VLO2xrFmJis1peTHKQsbOAztP1RIzH2++ZgyXi3
8QnvecMNCdrC8HKNSL/nsnw0XFzRLA4raohybiWgc+LD4gEtabynU7kZ5+xzkWkf
7kY8X4O32JXYKYH/f1L7nrec/T+Mhm1/HLLgCHR4dvjvlyHQaTO1F+6kb1elKR9O
hcw=
-----END CERTIFICATE REQUEST-----
Fingerprint:
c6:71:37:db:cd:ca:79:21:0c:5e:1e:a3:92:4f:b0:10:f7:63:56:eb (sha1)
05:64:22:fc:9f:01:a9:25:f8:bd:fd:f6:57:55:37:bd (md5)
juniper@SRX210-1>
juniper@SRX210-2> request security pki generate-certificate-request certificate-id srx210-2 domain-name srx210-2.blackhole-networks.com subject "CN=srx210-2.blackhole-networks.com,OU=VPNs,O=Blackhole-Neworks,L=Stuttgart,ST=Baden-Wuerttemberg,C=DE"
Generated certificate request
-----BEGIN CERTIFICATE REQUEST-----
MIIC/jCCAeYCAQAwfDERMA8GA1UEAxMIc3J4MjEwLTIxDTALBgNVBAsTBFZQTnMx
GjAYBgNVBAoTEUJsYWNraG9sZS1OZXdvcmtzMRIwEAYDVQQHEwlTdHV0dGdhcnQx
GzAZBgNVBAgTEkJhZGVuLVd1ZXJ0dGVtYmVyZzELMAkGA1UEBhMCREUwggEiMA0G
CSqGSIb3DQEBAQUAA4IBDwAwggEKAoIBAQC0W7SPPcf8LT2VzIJmPWMu11lxC914
TS3nvWG+MO7fjEgUbaPtxIHeejbL6X8LkNCBT1YkxSIUtMnc4yvaYlvY3un+s1QJ
6a1o/w91AFV9JCJQ5+DZroCkOXxkOolz9mt0cIpqTZ54EAsrvgc0ecgpRCSiNi0K
6WDnUn19UWYY6h1crjXLwRHQ6m+itNpw7LyB9cScTdNuI/v5dznc0S02/4p9OddT
dtq7Rl062Ru/VA4DTOy3vrU7+wf3ViLyGXDqDt6/lBYHj9xJHCBheb5DBkl0tVc/
Z/PdA5HXz+suv74J7h+gE4ekFCHanSIwUpNBJUuaDVgDPP+7lneow3cxAgMBAAGg
PTA7BgkqhkiG9w0BCQ4xLjAsMCoGA1UdEQQjMCGCH3NyeDIxMC0yLmJsYWNraG9s
ZS1uZXR3b3Jrcy5jb20wDQYJKoZIhvcNAQEFBQADggEBAKlpuczIqPbS/vti7pYr
0bf6I3qesY4b26m0+05o5S8l4/DdKHIQ7eZ8bvRFsV6q5jrTEGCLK3sYI4GHQ8Qc
WL8/f6TBLtro17TGcrJNy3Z2ZN+7nhWsfSLlJw7KTIzCPoJp5zk+AEd0XOoOt8yh
6XFtrTXHv9CD0OO2EB+hk4Ou30d5LJdpTJ7ch+8dkk+cI1Lrx8qHeanFbUheHN4B
Gkt5yhZqTKKlEWSJ9AahZMT10Bhc2YKqpot5i0u2cvLGLnqdiim9VLmZznCdfeyw
amUJs6XMrKO7BhHw32Zep7PwlvItGCWtwQ+6MtwfZYznYGkFOooWmiPjF4HaTR0a
x18=
-----END CERTIFICATE REQUEST-----
Fingerprint:
2f:f1:44:0c:d5:73:cb:03:ef:32:54:66:4d:de:d5:7c:ca:91:06:4d (sha1)
3e:dd:0d:07:6a:42:22:1c:ae:bd:ab:c5:00:bb:da:40 (md5)
juniper@SRX210-2>
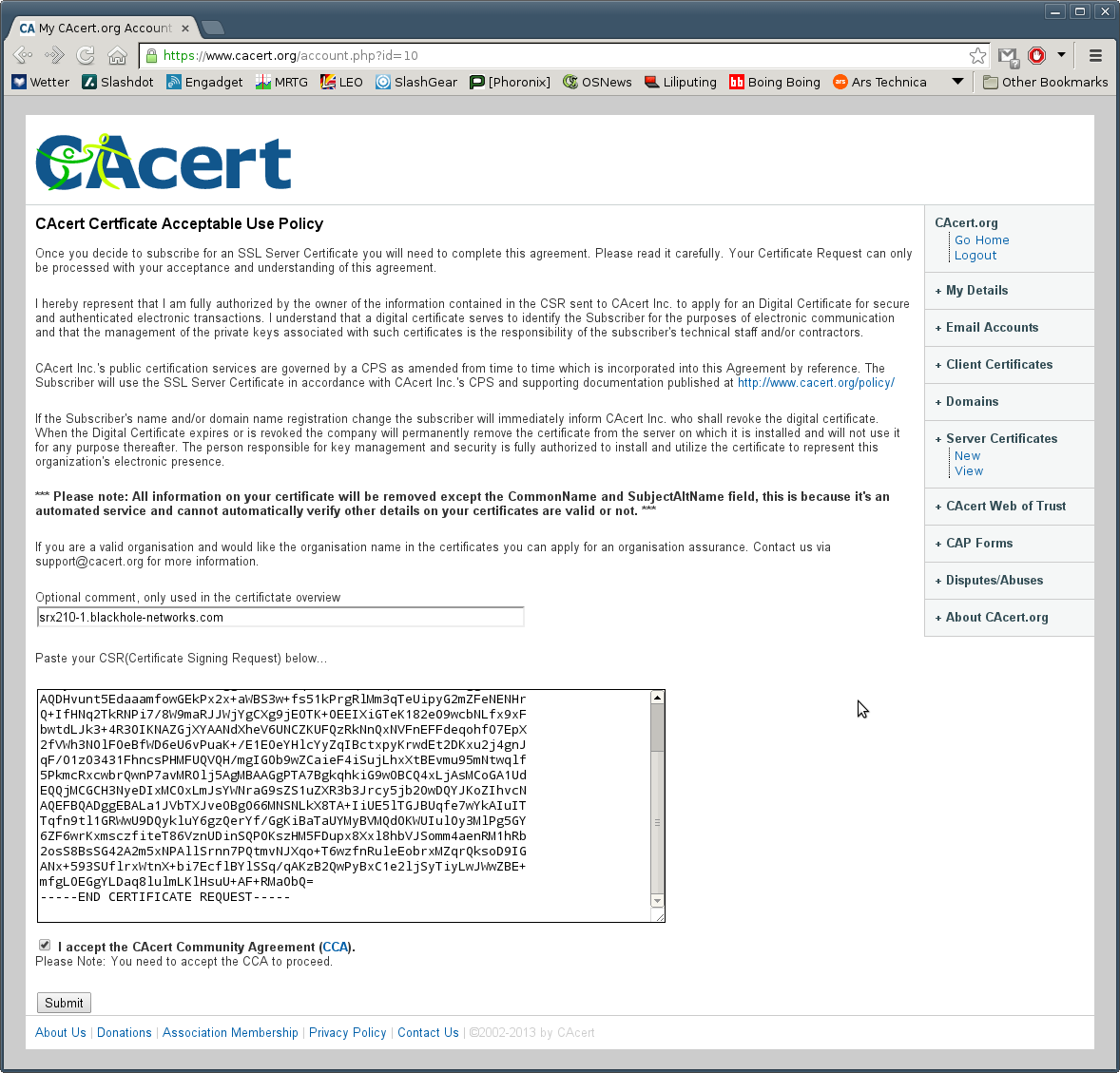
Now navigate to www.cacert.org and login to your account. Request a "New Server Certificate". Paste your CSR data into the web browser and submit for a new certificate.
Save the certificate to a file.
juniper@unix-box:~$ echo "-----BEGIN CERTIFICATE----- > MIIFkDCCA3igAwIBAgIDDd+4MA0GCSqGSIb3DQEBBQUAMHkxEDAOBgNVBAoTB1Jv > b3QgQ0ExHjAcBgNVBAsTFWh0dHA6Ly93d3cuY2FjZXJ0Lm9yZzEiMCAGA1UEAxMZ > Q0EgQ2VydCBTaWduaW5nIEF1dGhvcml0eTEhMB8GCSqGSIb3DQEJARYSc3VwcG9y > dEBjYWNlcnQub3JnMB4XDTEzMDkzMDA4NDkwOVoXDTE0MDMyOTA4NDkwOVowKjEo > MCYGA1UEAxMfc3J4MjEwLTEuYmxhY2tob2xlLW5ldHdvcmtzLmNvbTCCASIwDQYJ > KoZIhvcNAQEBBQADggEPADCCAQoCggEBAMe+6e3kR1ppqZ+jAYSQ/HbH5pYFLfD5 > +znWQ+uBGUybepN5SKnIbaZkV40Q0etD4h8c2rZORE0+Lv/xb2ZpEklaNiAJeD2M > TRMr44QQheIZN4rXzZ473Bxs0t/H3EVvC10smTf7hHc4go0BkaNdgAA11eF5XpQ0 > JkpQVDNGQ2dDE1UWcQUV16qiF/TsSlfZ9VaHc06UXR4F9YPp5Tq8+5or78TUTR5g > eVxjJmogFy3GnIqvB0S3YMrG7aPiCcmoX/TXPTfjfUWGdyw8cwVRBVAf+aAgY5v3 > BkJqJ4XiJK6MuHFe0ES+a73mY23CqV/k+SZxHFzButDCc/tq8xE6WPkCAwEAAaOC > AW4wggFqMAwGA1UdEwEB/wQCMAAwDgYDVR0PAQH/BAQDAgOoMDQGA1UdJQQtMCsG > CCsGAQUFBwMCBggrBgEFBQcDAQYJYIZIAYb4QgQBBgorBgEEAYI3CgMDMDMGCCsG > AQUFBwEBBCcwJTAjBggrBgEFBQcwAYYXaHR0cDovL29jc3AuY2FjZXJ0Lm9yZy8w > MQYDVR0fBCowKDAmoCSgIoYgaHR0cDovL2NybC5jYWNlcnQub3JnL3Jldm9rZS5j > cmwwgasGA1UdEQSBozCBoIIfc3J4MjEwLTEuYmxhY2tob2xlLW5ldHdvcmtzLmNv > baAtBggrBgEFBQcIBaAhDB9zcngyMTAtMS5ibGFja2hvbGUtbmV0d29ya3MuY29t > gh9zcngyMTAtMS5ibGFja2hvbGUtbmV0d29ya3MuY29toC0GCCsGAQUFBwgFoCEM > H3NyeDIxMC0xLmJsYWNraG9sZS1uZXR3b3Jrcy5jb20wDQYJKoZIhvcNAQEFBQAD > ggIBAKnusrTv4owKxPduAvMDjWqNMgnRGvo3ANJOreuRI4NQb9GtEVzMqg5y5XKv > X8cXiHsyXnQju0a2CkKxrn+1HbLOp3wvtpzb1bj99s5H7wrGMbMsOZiVecsiIeSs > fwD+dkP4ZtrO3ClpU5PXceQ9Dw2sFh8Nmd66M/Y640OII8XKfKKRtSqhsG8ZPUBr > 2wFN/oZGVfm0eJleeJzM6kCZYLhaBTDUki+pSPLOogpcc8gFdvVyIcXeFz5nMD8F > vuf26gInaH3U04XX1tyBRuOaOr/5xhVANBEd7XqSY8Z9Q0Vvx/jRFikspwq9XgbE > HSZu2gqCNrUJN1+myX5Avrga/k76ASDJN55Hl4k3bma7f2DXHURsOkTCz+v8ZalH > F29rlpTwqe5rPwQHk7dFxF7jOwL2cmQz4fwWayyGFvmQxwsO+X86oc0LUwLE6Tp4 > WlA5poMAfuJ+y9ctmFN/QTIpJvWI64OtdOMxZevwNRuUtgHAS5KBZU0Fss2GLEE5 > 1ILCMtmBHffyuG9TPGURzwv6TasOSxW16XSNL3hOhpoDzWleCqC8zIRkumVxOf+5 > KH/Es6BMfrnCjcYWZf+5MchUcs1Z9s6oCA11q1O6WkDmuuZwX1MFaqvHhKFBM7YU > JfgYA+jDeLQmILKkgkqgobH6cCIYcCVHWfBV/VlYRla2CznA > -----END CERTIFICATE-----" > srx210-1.pem
Check that the certificate is valid. Note that the CAcert root cert needs to be installed as a trusted CA for this to work (or the root cert needs to be referened in the openssl command).
juniper@unix-box:~$ openssl verify srx210-1.pem srx210-1.pem: OK juniper@unix-box:~$
Then copy it up to the matching SRX.
juniper@unix-box:~$ scp srx210-1.pem juniper@10.0.110.211: srx210-1.pem 100% 1988 1.9KB/s 00:00 juniper@unix-box:~$
Load the certificate up into the SRX.
juniper@SRX210-1> request security pki local-certificate load certificate-id srx210-1 filename srx210-1.pem Local certificate loaded successfully
Verify that the cerfificate is OK on the SRX.
juniper@SRX210-1> request security pki local-certificate verify certificate-id srx210-1 Local certificate srx210-1 verification success juniper@SRX210-1>
Repeat the steps for the other SRX: CSR, certificate, etc. If something doesn't verify at any point, backup and fix!

